Remote Desktop security is crucial due to the growing need for remote access. Vulnerabilities such as weak passwords and open RDP ports can lead to Brute-force and DDoS attacks.
So, you should implement Security solutions such as using two-factor authentication, restricting Users’ access, and enabling network-level authentication.
However, having a powerful RDP server and using it to perform remote tasks can significantly reduce the need for RDP Security Best Practices.
Is RDP Secure?
By default, RDP has weaknesses that make it an attractive target for hackers:
- Simple authentication method (username and password)
- Default open port 3389
- Possibility of Session ID theft or session hijacking by the user
- Possibility of accessing other network systems with tools such as Mimikatz and Pass-the-Hash
- Possibility of remote code execution (BlueKeep)
RDP, as a standalone technology, is not secure enough. To protect data and remote connections, additional security measures must be supplemented with RDP server.
Also, you can buy RDP from a reliable provider to implement better security measures to ensure more secure remote connections and protect your system from any cyber-attacks.
Best Practices for Securing Remote Desktop
This section introduces proven solutions for strengthening remote desktop security. Implement them step by step to achieve the security you expect.
1. Use Long and Complex Passwords for RDP
Accounts used for remote connections should be a challenging target for hackers.
Using unique, hard-to-guess passwords for these accounts can ensure that your first line of defense against RDP is highly resistant to cyberattacks.
So try to define your RDP account password according to the following principles:
- Use long passwords (at least 10 characters).
- Use a combination of uppercase and lowercase letters, numbers, and special characters.
- Avoid using common words or information that is easy to guess, such as your birthday.
- Do not use duplicate passwords for accounts and services.
- Use a password manager.
- Disable automatic password saving in RDP software.
- Change passwords periodically.
2. Restrict Remote Desktop access to specific users
Allowing every user to connect to a remote desktop poses a security risk.
Therefore, restrict the admin accounts allowed to connect to a remote server via Remote Desktop.
To do this, you can try the following three solutions:
1. Remove the Administrators group from RDP logon settings
All administrator accounts can log in via RDP by default, but this access can be dangerous if not properly managed.
To improve security, remove the Administrators group by following the steps below and keep only the Remote Desktop Users group.
- Open the Local Security Policy.
- Go to the following path:
Local Policies > User Rights Assignment > Allow logon through Remote Desktop Services
- Select the Administrators group from the Local Security Settings tab and click Remove.
- Leave the Remote Desktop Users group unchanged.
2. Create a dedicated group for RDP access
- Open Local Users and Groups.
- Click on Groups to create a new group for remote access.
- Add the desired accounts to this group.
- Next, assign this group for remote access in the Allow logon through Remote Desktop Services section of the Local Security Policy.
3. Restrict access with a firewall
Enabling the IP whitelisting feature on the firewall permits only specific and trusted IP addresses to connect to RDP.

3. Use Network-Level Authentication (NLA)
NLA provides an additional form of identification, such as smart cards, one-time passwords, or biometrics, which helps improve RDP security.
NLA is typically enabled by default in most versions of Windows, including Windows 11 and Windows Server 2022.
To ensure this:
- Open the Group Policy settings and go to the following path:
Computer\Policies\Windows Components\Remote Desktop Services\Remote Desktop Session Host\Security
- Enable the following option:
“Require user authentication for remote connections by using Network Level Authentication.”
- From the remote system, go to the System Properties section.
- Go to the Remote tab.
- Check the following box:
“Allow connections only from computers running Remote Desktop with Network Level Authentication.”
Important: If the RDP client runs on a system that does not support NLA, you may need to configure the remote server to accept connections without NLA. However, disabling NLA reduces security, so it should only be done if necessary.
4. Implement Two-Factor Authentication (2FA)
2FA forces users to go through another login process after their primary password, which can be complicated.
The most common 2FA method is to enter a code sent to an Authenticator app integrated with the RDP setup.
5. Set an account lockout policy
Attacks such as brute force begin with several attempts to guess a password. To prevent this, you can activate the automatic account lockout feature after a few attempts, ensuring that the hacker or bot does not have enough time to try other passwords.
You can use the Group Policy app to set the account lockout policy.
- Open this app and go to the following path:
Computer Configuration > Policies > Windows Settings > Security Settings > Account Policies > Account Lockout Policy
With the three options available, consider the desired limit for the Lockout Policy:
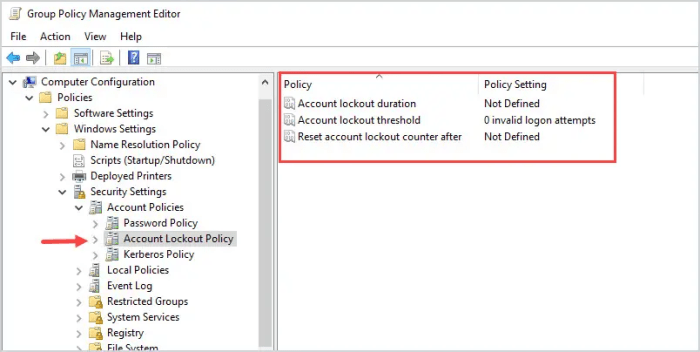
Account lockout duration – the duration of the user account being locked after reaching the allowed number of failed login attempts
Account lockout threshold – the number of allowed failed login attempts
Reset account lockout counter after – the duration after which the failed login attempts are reset (if the threshold has not been reached)
6. Keep your operating system and remote desktop software up to date
Fortunately, RDP, as a tool integrated with Windows, is automatically updated with the latest Windows security fixes on a standard cycle.
Since these updates aim to enhance performance and security, always strive to install the latest operating system patches. These patches replace security vulnerabilities in older versions with new improvements.
7. Use VPNs for Secure RDP Connections
VPN creates a secure tunnel for RDP traffic, making it challenging for hackers to trace data and connections. Therefore, installing a reliable VPN on local and remote machines can greatly enhance the security of remote access connections.
You can set up a VPN for RDP server by following these steps:
- Choose a trusted and secure VPN provider.
- Install and configure the VPN on the client and remote machine.
- Connect to the VPN before making RDP connections.
8. Monitor user sessions
Hackers start unusual activities by infiltrating the system, and by identifying them in time, you can prevent bigger risks. So try to track the status of sessions and follow the following signs:
- Successful logins from unexpected locations or at unusual times
- Increased resource consumption
- A sudden increase in network traffic for no apparent reason
- Abnormal manipulation of sensitive files
- Suspicious connections to external servers
- Adding new accounts with admin access
- Removing authorized users from security groups
- Unknown processes or high CPU and RAM consumption
- Executing scripts and remote management tools without permission
In these situations, it is essential to enforce the necessary security measures, including managing sensitive files, limiting access to sensitive resources, and disabling Clipboard Redirection.
You can also manage sessions effectively with these two solutions:
– Set the Idle Timeout period to close sessions automatically after a specified period of inactivity.
– Specify a maximum duration after which users will be required to re-authenticate.

9. Disable RDP if not in use
Generally, disable any features and programs that you are not currently using. This rule also applies to RDP, as keeping it enabled increases the attack surface and reduces system security.
What Are The Main Security Vulnerabilities Of RDP?
Remote Desktop, a built-in Windows tool, has sufficient security, but this security is not 100% guaranteed.
Weak passwords, outdated systems, open ports, and insufficient authentication are among the vulnerabilities that can lead to more serious issues, the main ones of which are outlined below:
- Executing brute force attacks and unauthorized intrusions into remote systems
- Intercepting communications between users and servers through MITM attacks
- Stealing authentication information via phishing attacks
- Installing ransomware to extort payment in exchange for sensitive information and data
- Occupying remote servers with DDoS attacks
- Infiltrating through software vulnerabilities
- Utilizing open ports for remote attacks
- Executing shellcode or malicious payloads
These security issues necessitate careful management to reduce the risks they present. Therefore, you should approach RDP security improvement methods seriously.
Conclusion
Remote Desktop (RDP) is a Microsoft communication protocol essential for remote communications. By buying RDP and enhancing its security through strong authentication, limiting RDP access levels, and keeping system software updated, you can significantly improve the security and performance of remote connections. This lets you focus on your primary goals without worrying about data or information leaks.